If you run a site with HTTPS, the first thing you’ll want to do is make sure that the Certificate and Web Server are set up correctly.
A great tool for testing your Certificate and Server Configuration is SSL Server Test by Qualys SSL Labs. Using their site all you have to do is enter your domain name and they run various tests on your SSL Certificate and give you a grade based on the results.
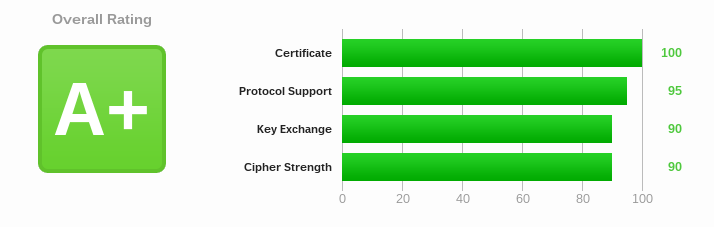
When you test your site you are looking to get at least an A-, however, more important than your score are the warnings and errors the site offers. And while it is possible to get an A+, it isn’t always the best idea to aim for this. You should consider the trade-off between devices that your site supports and the potential security implications. For example, Google and Facebook only get a B because they support certain protocols that are ‘weak’ or ‘insecure’ in order to still support a large array of older devices.
Report Details
Summary
The summary shows your current score as well as any issues or warnings that your setup might have triggered.
Errors
Any item in red is a serious issue and you should fix immediately.
Some common errors include:
This server is vulnerable to the POODLE attack. If possible, disable SSL 3 to mitigate. Grade capped to C.
This means that your server is vulnerable to the POODLE attack. The easiest solution is to disable SSL 3 on your server. More Information
This server supports anonymous (insecure) suites (see below for details). Grade set to F.
This means that some of the Cipher Suites that you’re using are considered insecure. You should look in the Cipher Suites section of the report and remove any that are marked ‘INSECURE’.
Warnings
The report will also return warnings. These are things that should be corrected, but are not vital at this point in time to the security of your site. Some of these may have trade-offs that should be considered when correcting making corrections.
Some important warnings to look for are:
Certificate uses a weak signature. When renewing, ensure you upgrade to SHA2.
This means that your Certificate is most likely using SHA1 signatures and should be upgraded to SHA2. This requires you to get a new certificate with an SHA2 signature. This particular warning indicates that your certificate will expire before browsers start issuing errors for this, so it’s possible to wait until you need to renew to correct this. Most Certificate Authorities will allow you to re-issue your certificate for free to one with SHA2 and usually have a tool to help you re-issue. This will vary by the Certificate Authority that you use. More Information.
Certificate has a weak signature and expires after 2016. Upgrade to SHA2 to avoid browser warnings.
This warning is the same as the one above, but your certificate expires after browsers will start issuing errors about this. You should re-issue your certificate with your Certificate Authority. More Information.
This server’s certificate chain is incomplete. Grade capped to B.
This warning means that you need to include the Intermediate Certificates on your server. This will not cause an issue for most users, but should still be corrected. You should look up how to install an Intermediate Certificate for your web server, as each one is different.
This server accepts the RC4 cipher, which is weak. Grade capped to B.
The RC4 cipher is now considered weak and it is recommended not to use it. However, some PCI compliance tests may require you to use it to mitigate the BEAST attack. BEAST should no longer be a threat as it has been mitigated on the client side. Depending on your PCI compliance vendor, you may have no choice but to keep RC4 on for now even if it is the worse option.
Protocols
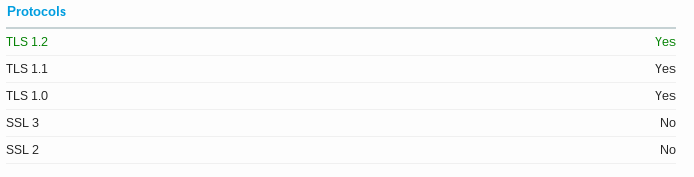
The protocol section lists the protocols the server supports. SSL should not be used as it is considered insecure. TLS is what your server should use, and it is best to be able to support all 3 versions currently available as many browsers currently do not support TLS 1.1 or TLS 1.2.
Cipher Suites
This is a list of the Cipher Suites used by your server. You should remove any listed as ‘INSECURE’ and consider removing any listed as ‘WEAK’.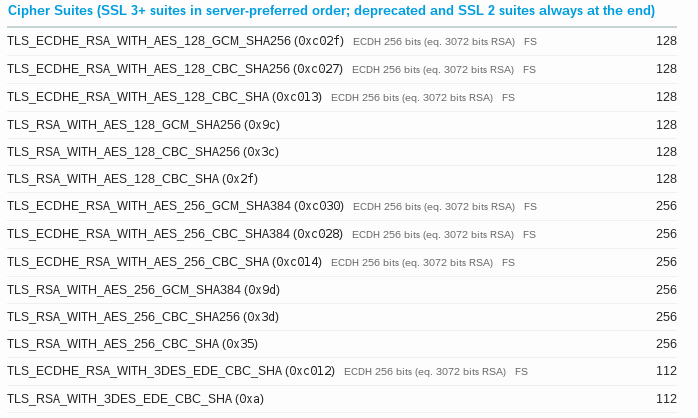
Handshake Simulation
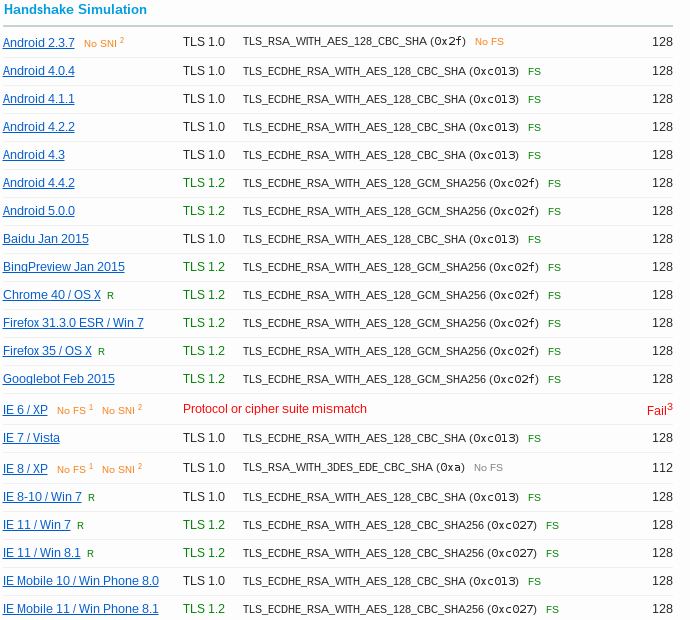
Handshake Simulation is most interesting part of the report in my opinion. It lists various devices and whether that device will work with your current server configuration. Here you can judge tradeoffs between particular settings and what changes would cause browser support to be lost. You can click on any browser and see what it supports and doesn’t support. IE 6 on Windows XP doesn’t support TLS, which means that since we disabled SSL 2 and 3 (see the Protocols section above) it will not be able to access the site over HTTPS.
In addition to the security implications, it’s also a good thing to disable SSL 3 as a means of forcing the few remaining users of IE 6 to upgrade their browser to access the a large part of the internet. Here at Hall, we have long ago stopped supporting IE 6 and even stopped supporting IE 7 in 2013.
Further Reading
- Mozilla Wiki: Security/Server Side TLS – Detailed information on configuration of TLS on a server.
- How To Install an SSL Certificate from a Commercial Certificate Authority
- Mozilla SSL Configuration Generator – A tool to generate common SSL configuration for various Web Servers
- IIS Crypto – Simple GUI tool to configure SSL configuration for IIS




